Launching a New Firm
Outgrowing DIY IT
Switching IT Providers
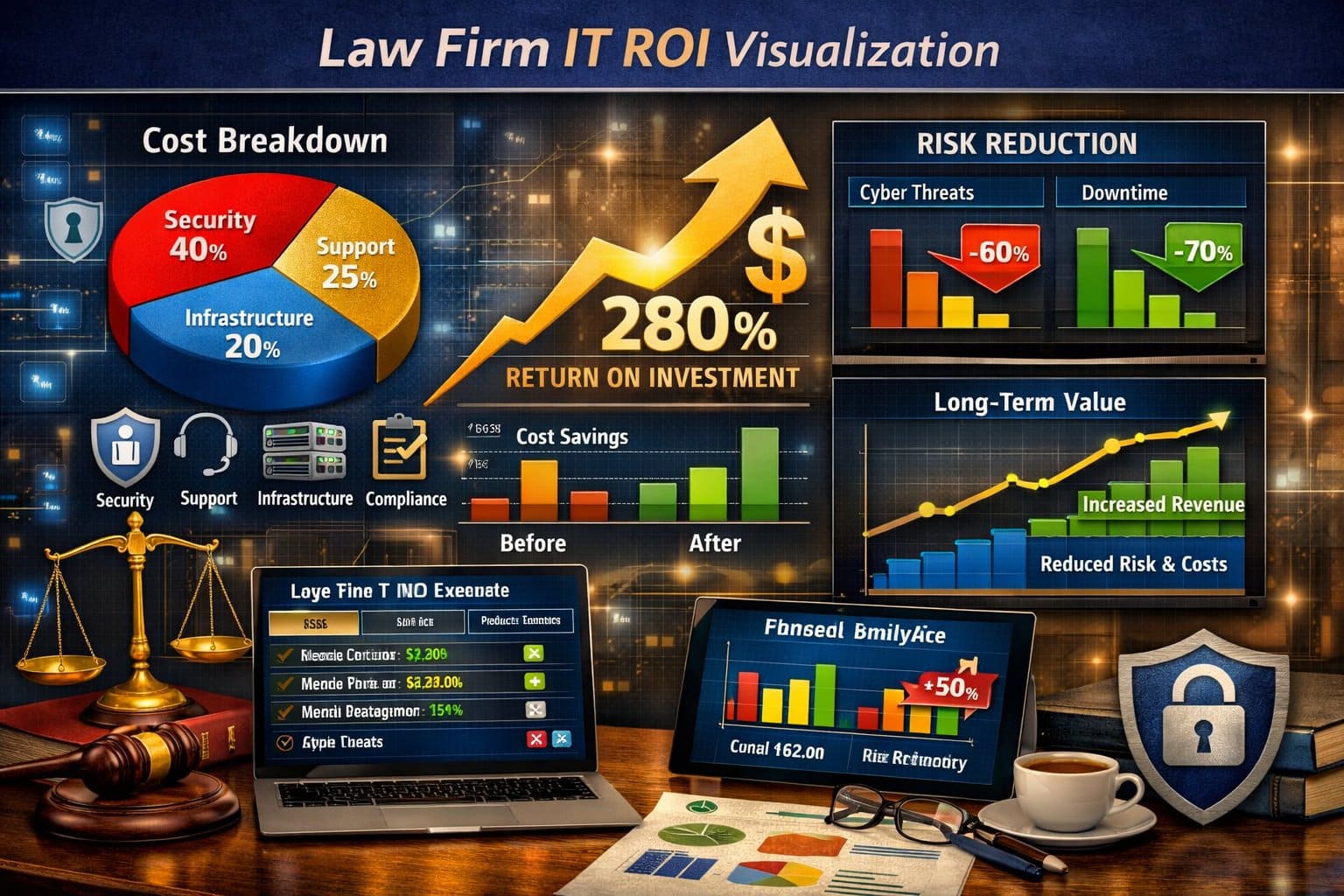
Why Security Now Touches Revenue, Risk, and Reputation
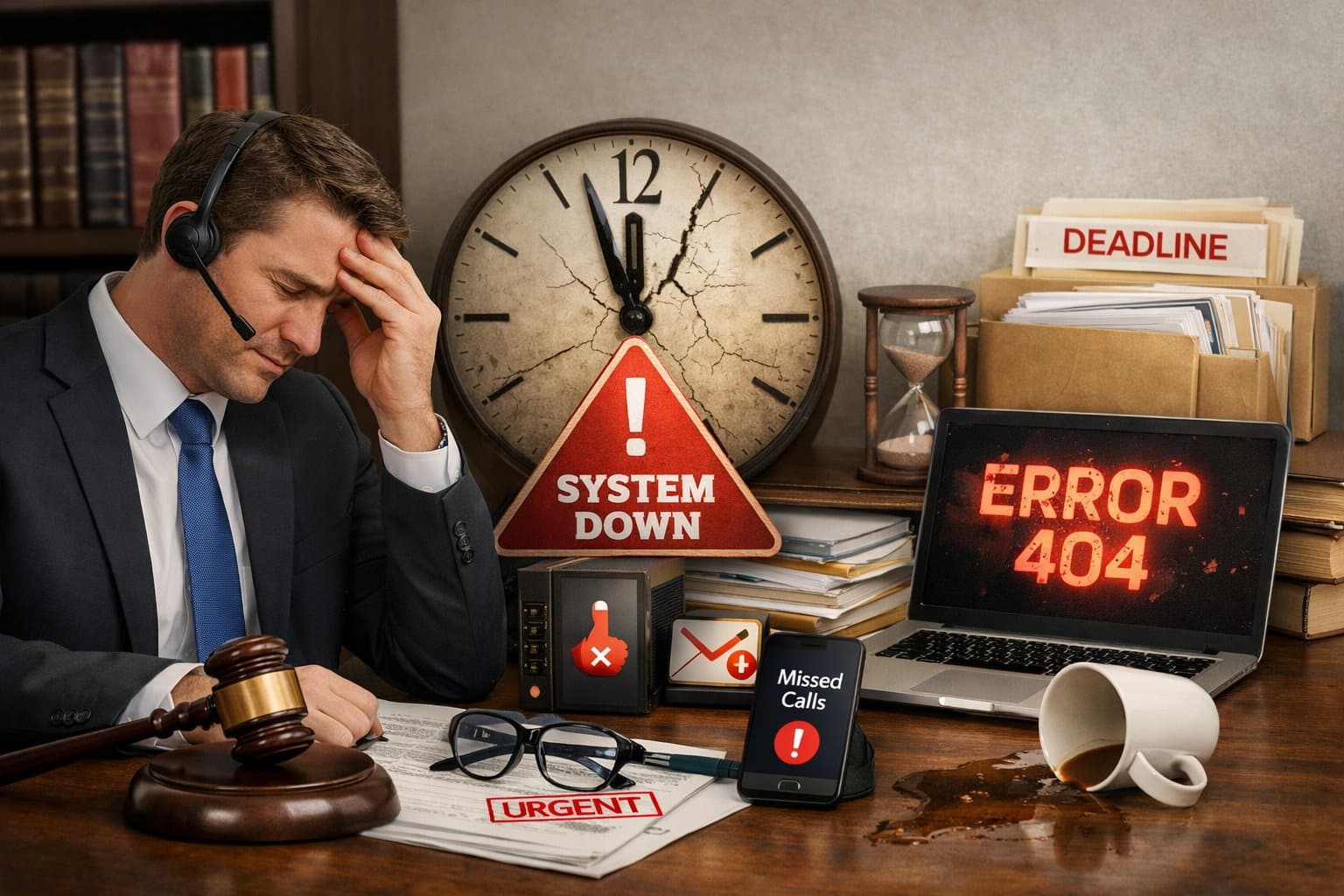
Downtime Burns Billable Hours
When systems are unreliable, someone in the firm has to step in.
Lawyers, owners, and admins get pulled away from billable work, and revenue starts leaking.
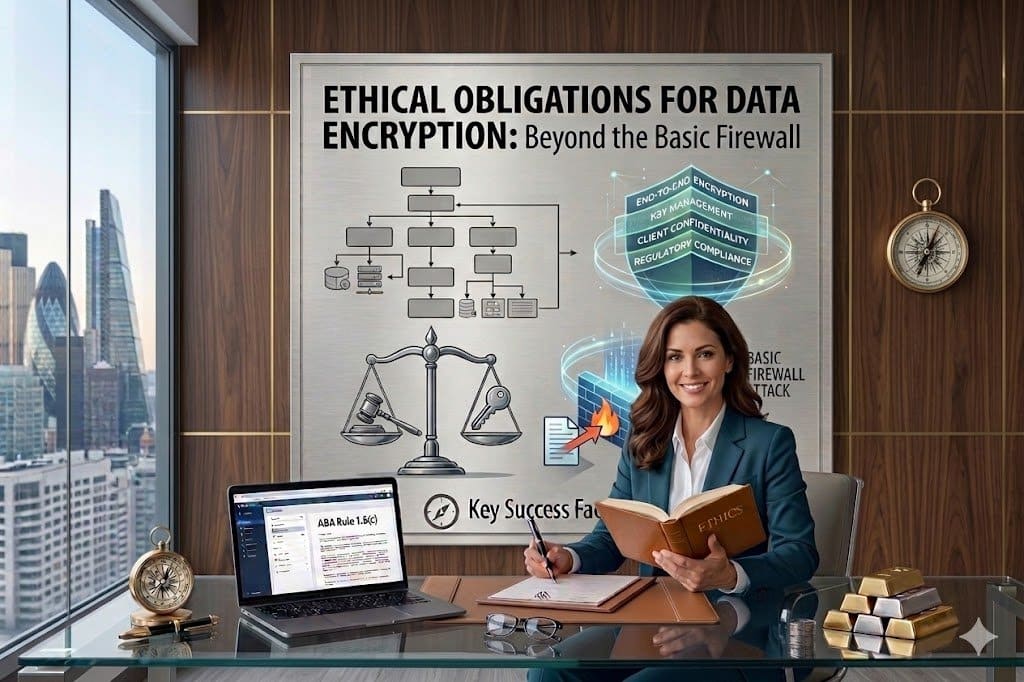
Confidentiality can't be best efforts
Your duty to protect client information – along with rising expectations from clients, regulators, and the ABA – demands secure systems, not duct tape fixes.
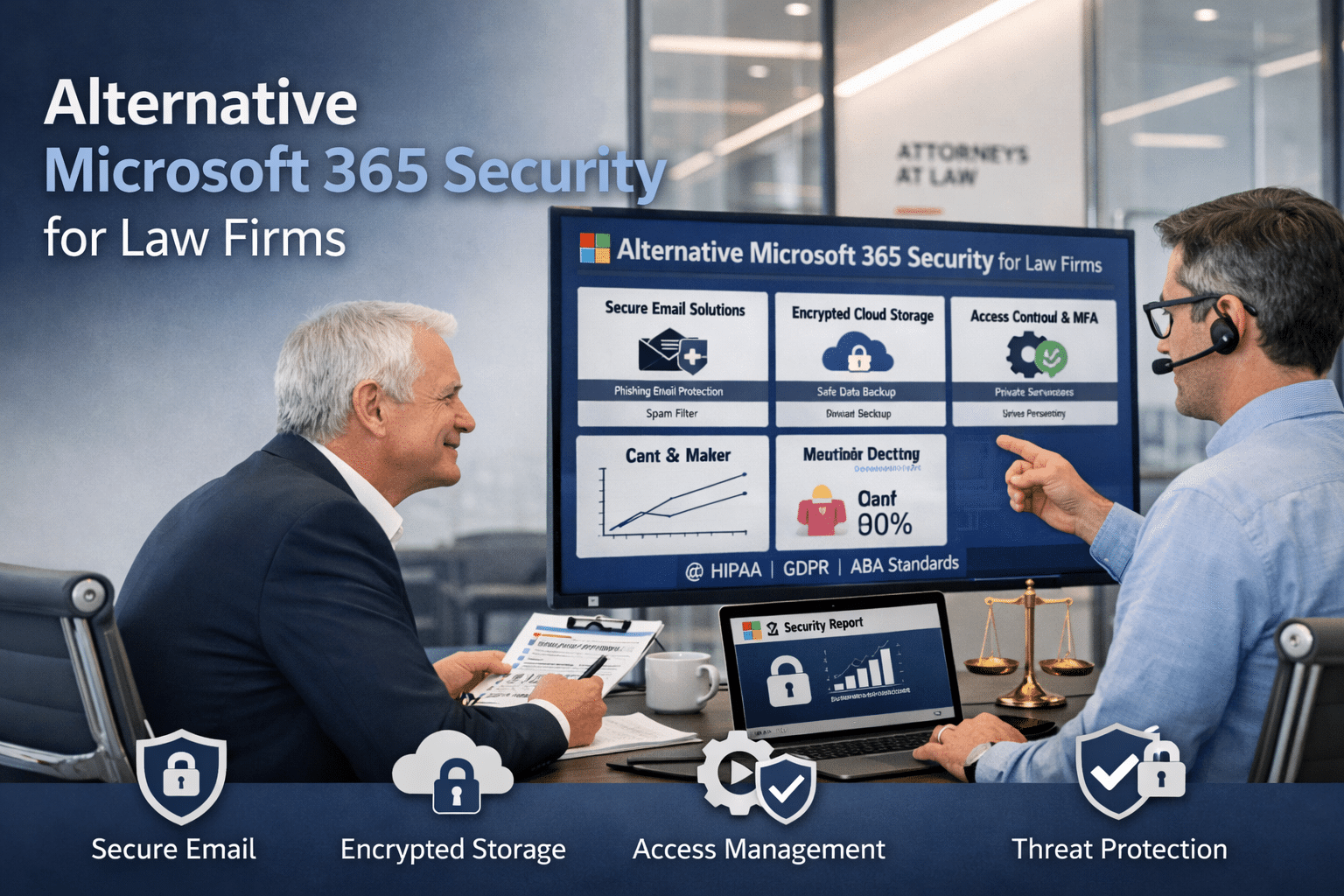
Cyber-Insurance is Getting stricter
When something goes wrong, insurers want proof that MFA, backups, and email protections were actually in place.
Ticking boxes on a questionnaire is no longer a strategy.
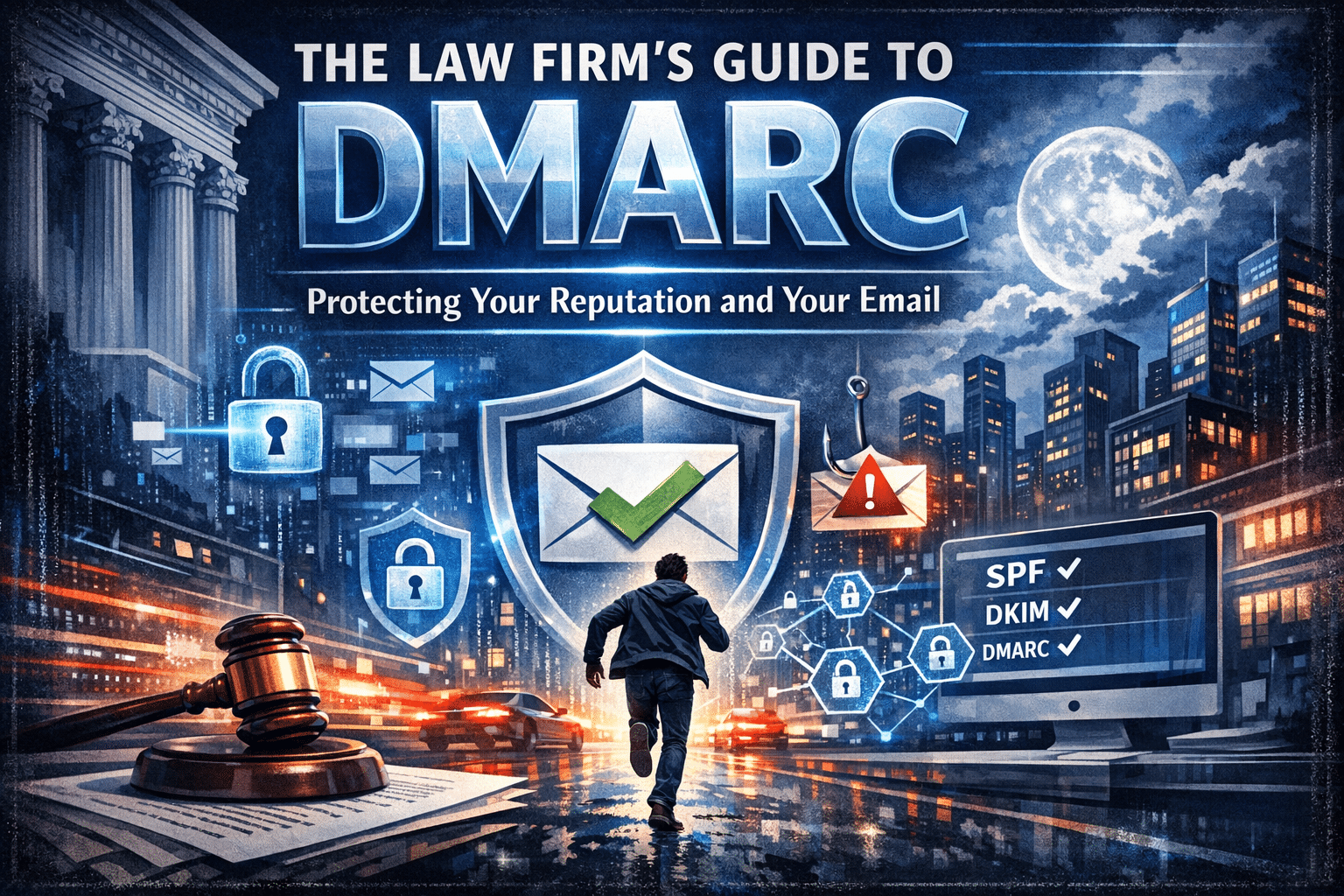
Email Impersonation is: The Front door
Many breaches begin with a fake email that looks real enough to fool your team, your clients, or your vendors and result in real financial consequences for your firm.

“MoreMax is true to their company name. They help law firms handle complicated IT issues that we have no business knowing so that we can focus on what matters. Serving our clients to our best abilities. Francois and his team have always been helpful and responsive with inquiries and questions. Highly recommend them.”

“MoreMax has taken everything IT-related off my plate, so that I can focus on what I need to focus on. They’re responsive, lovely to work with, and provide individualized attention.”

“As a solo practitioner, I’ve retained MoreMax to handle all of my IT needs, and it’s been one of the best decisions I’ve made for ensuring dependable technical support. They are attentive, knowledgeable, and consistently able to resolve issues efficiently. I highly recommend considering their services.”

“My business: My Locum Group needed to put a redundant intake system in place quickly, and because we operate in healthcare, security and reliability were both critical. Francois and the MoreMax team stepped in, helped us get that deployed, and also improved the baseline security across our systems. The result was a more stable and secure setup, with much greater peace of mind on our side. Francois and his team were responsive, knowledgeable, and easy to work with throughout. I would highly recommend MoreMax to any business looking for a dependable technology partner.”

“I am a US immigration attorney and am a client of Moremax. Moremax specializes in marketing for small and medium-sized law firms. The owner and my marketing manager provide excellent social media marketing and don’t insist on pouring money down the drain with Google and Facebook Ads. Above all, the service is affordable, the employees are friendly and the service is worthwhile.”
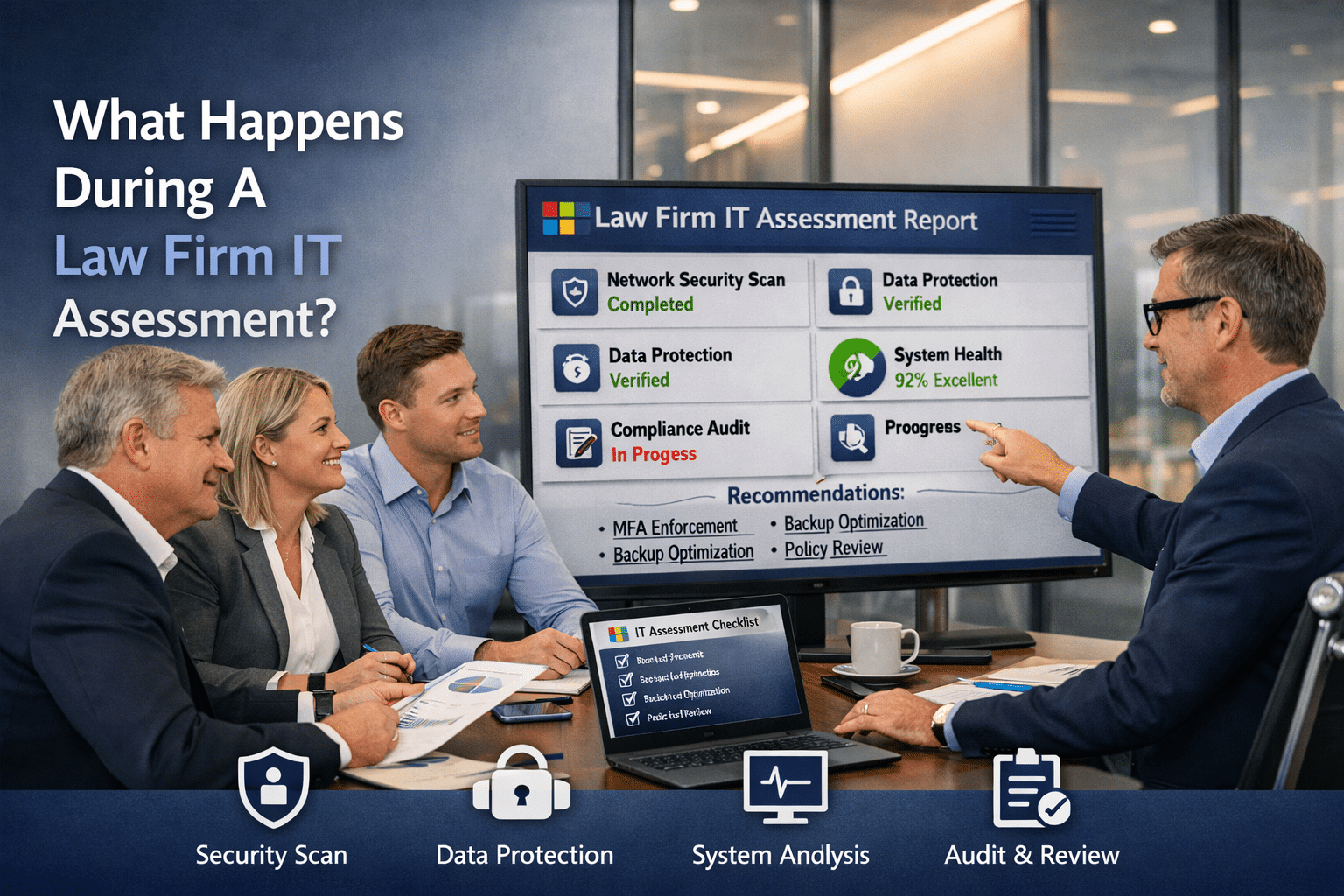
How Firms Get Started With MoreMax
Pay Only for What You Need
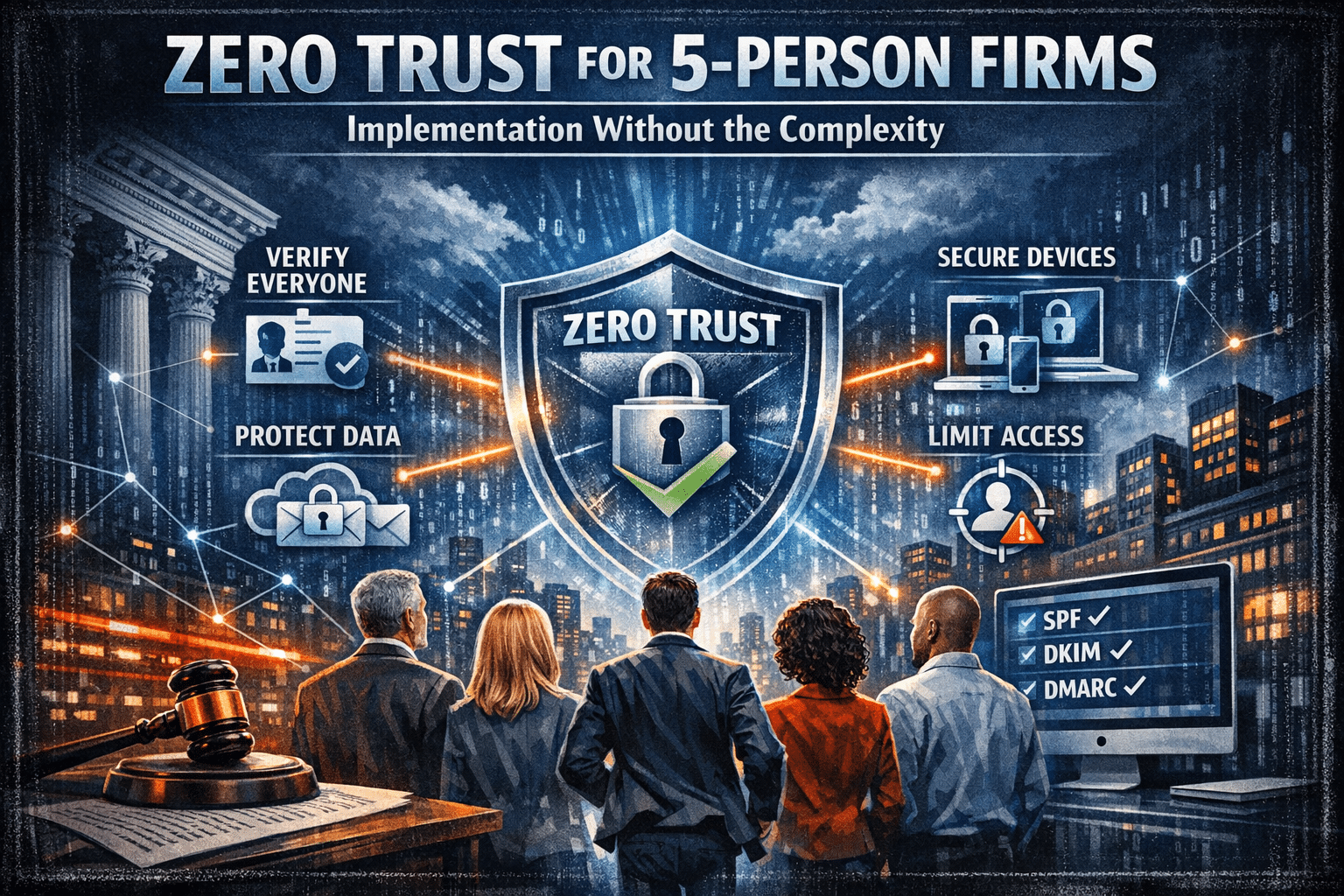
Designed around the security expectations law firms face today:
Cyber Essentials for Law Firms™
Everything your firm needs to protect email, files, and devices from ransomware and data loss — without paying for full helpdesk support. Simple. Secure. Compliant.
Modular IT Helpdesk Support
Choose the level of support that fits your firm. Exclude it if you prefer a security-only plan, add a set number of hours each month, or include full coverage in your service plan. Scalable, predictable, and built around the way your firm works.
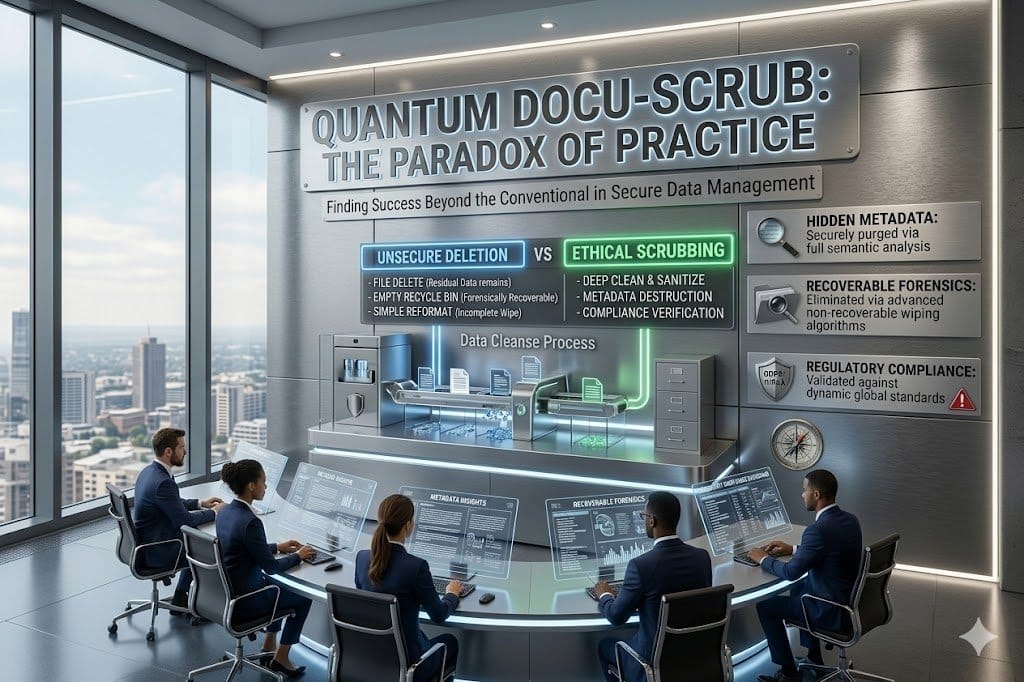
Email Impersonation Defense Suite
Ensure every message your firm sends is verified through DMARC, SPF, and DKIM —stopping spoofing, protecting client trust, and supporting compliance.
Cybersecurity Awareness Training
Quick, engaging sessions that teach your team to spot phishing, social-engineering, and ransomware attempts before they become breaches. (Required if you handle PHI or financial data, and expected under ABA ethics.)
In-House Web Design & Social Media
Your website and social presence should work as hard as you do. Our design team builds fast, elegant sites that convert — and our social packages keep your firm visible and consistent.
Practice Management & Legal Software Integrations
Your technology should work together, not in silos. We help connect and support key platforms like Microsoft 365, document storage, intake tools, e-signature, billing, and practice management software so your firm can work more efficiently, stay organized, and reduce double handling.
VoIP & Communication Systems
Stay connected from anywhere — office, home, or court. We set up and manage modern VoIP phone systems (like Teams or 3CX) with secure call routing, voicemail-to-email, and mobile extensions. Clear calls, simple setup, and predictable costs.
Passionate – Dedicated – Professional
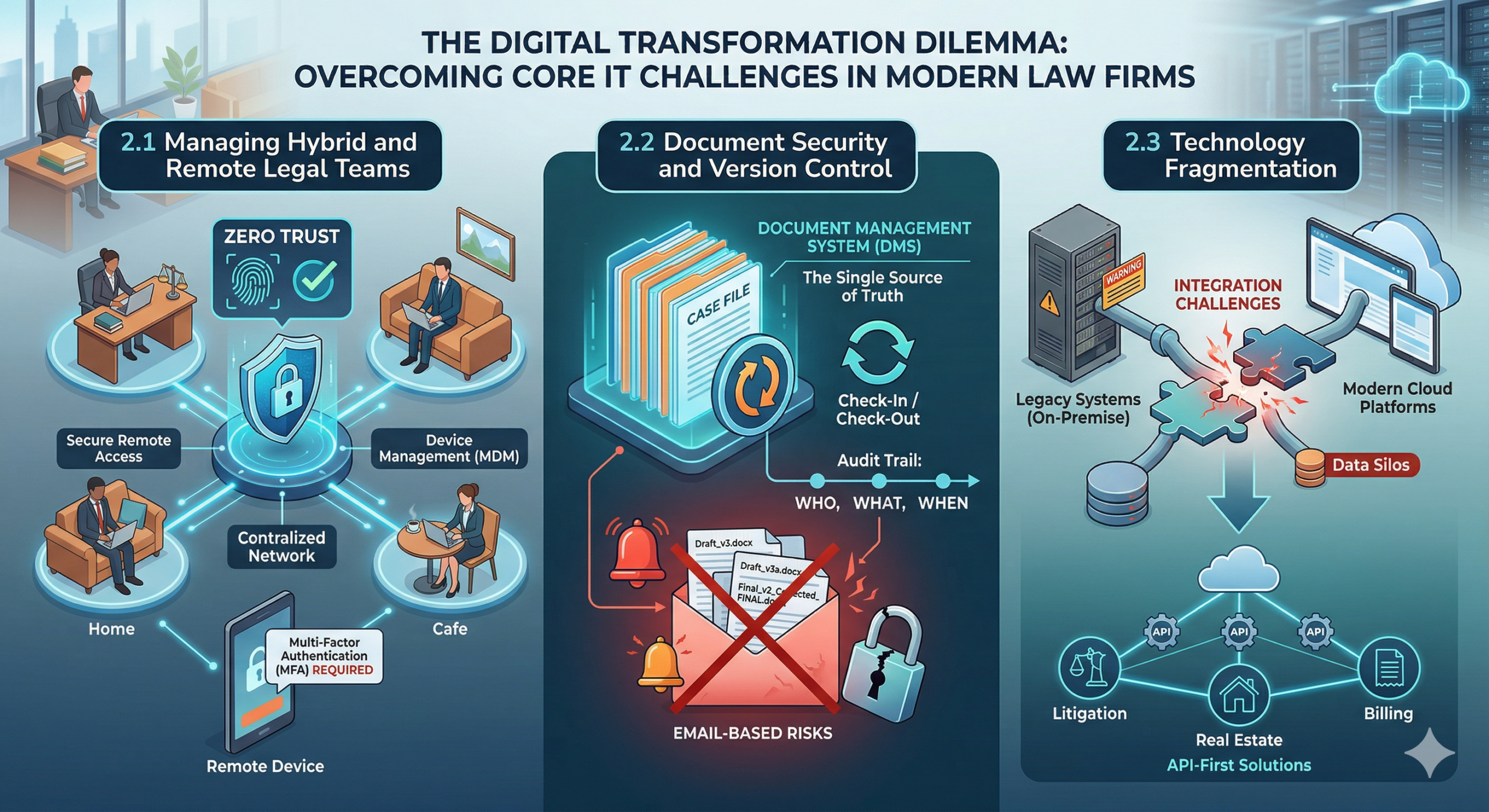
latest news & insights
We’re committed to staying ahead of the curve, constantly tracking the latest developments, trends and insights so we can bring you fresh, relevant information that helps your practice thrive. Whether it’s legal tech, content strategy, client-expectation shifts or regulatory changes, we’ve got you covered with concise, actionable updates. Let’s keep moving forward together.